Certificates of Destruction
Verifiable proof of secure data destruction for compliance and audit purposes
What's Included
Each certificate includes:
- Unique certificate number
- Verification code for online validation
- Device serial number and MAC address
- Drive model and serial number
- Wipe method used and number of passes
- Start and completion timestamps
- SHA-256 verification hash
Verify & Download Certificate
After a successful wipe, you'll receive a verification code displayed on screen. Create an account and verify your certificate to download an official PDF:
Verify CertificateEnter your verification code and device serial number to authenticate and download your official Certificate of Data Destruction.
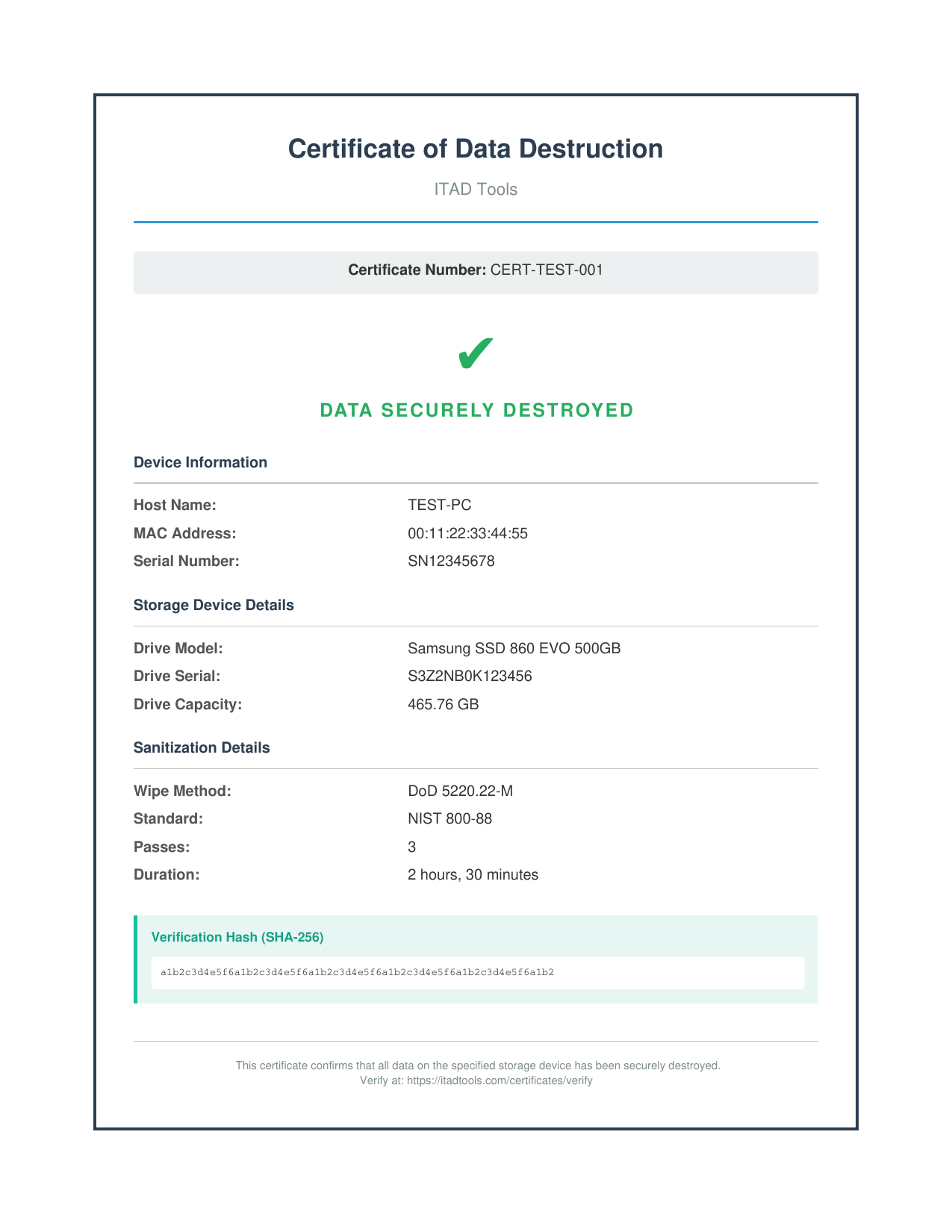
Sample Certificate of Data Destruction